Development of Suspicious Address Blocking System
A suspicious address blocking system is the first line of AML defense. Its task: prevent interaction with known bad actors before a transaction reaches the protocol or exchange. For DeFi protocols, this also reduces regulatory risks in jurisdictions where regulators are beginning to focus on on-chain compliance.
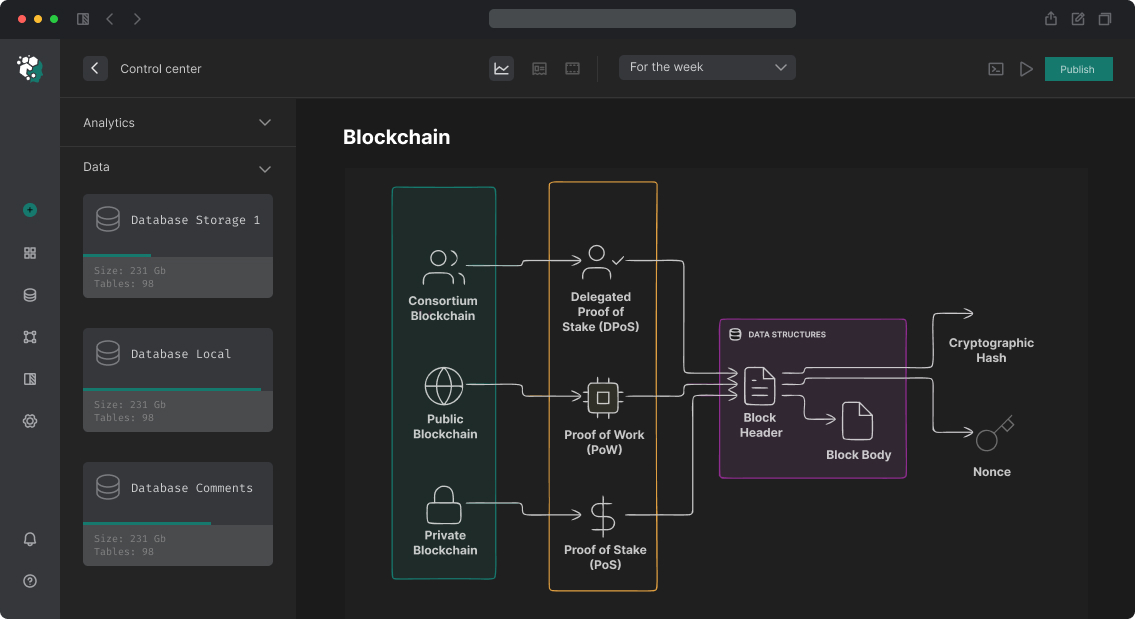
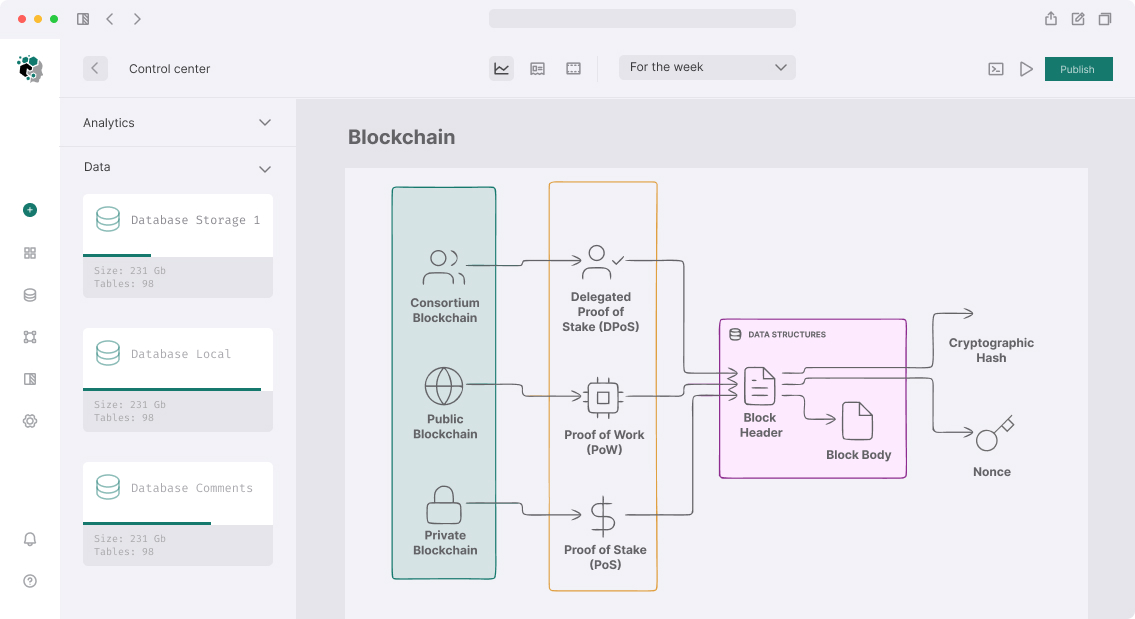
Blocklist System Architecture
On-chain blocklist (for smart contracts)
contract AddressBlocklist {
// Management via multisig or governance
address public admin;
mapping(address => bool) public blocked;
mapping(address => string) public blockReasons;
event AddressBlocked(address indexed addr, string reason);
event AddressUnblocked(address indexed addr);
function blockAddress(address addr, string calldata reason) external onlyAdmin {
blocked[addr] = true;
blockReasons[addr] = reason;
emit AddressBlocked(addr, reason);
}
function blockBatch(address[] calldata addrs, string calldata reason) external onlyAdmin {
for (uint i = 0; i < addrs.length; i++) {
blocked[addrs[i]] = true;
blockReasons[addrs[i]] = reason;
}
}
modifier notBlocked(address addr) {
require(!blocked[addr], string.concat("Address blocked: ", blockReasons[addr]));
_;
}
}
// Usage in protocol
contract Protocol is AddressBlocklist {
function deposit(uint256 amount) external notBlocked(msg.sender) {
// deposit logic
}
}
Off-chain blocklist (for exchanges and services)
For high-load systems — Redis Bloom Filter for fast membership checking:
class AddressBlocklistService {
private bloomFilter: RedisBloom;
private exactBlocklist: Set<string>;
async isBlocked(address: string): Promise<BlockStatus> {
const normalized = address.toLowerCase();
// Bloom filter: false positives possible, false negatives impossible
if (!await this.bloomFilter.exists(normalized)) {
return { blocked: false }; // quick answer: definitely not in blocklist
}
// Exact check to confirm (bloom filter could give false positive)
const exactMatch = await this.db.findBlockedAddress(normalized);
if (!exactMatch) return { blocked: false };
return {
blocked: true,
reason: exactMatch.reason,
source: exactMatch.source,
addedAt: exactMatch.addedAt,
};
}
async updateFromSanctionsList(): Promise<void> {
// OFAC SDN list (updates several times per week)
const ofacAddresses = await fetchOFACCryptoAddresses();
// Chainalysis Sanctioned Addresses list
const chainalysisAddresses = await this.chainalysis.getSanctionedAddresses();
const allNew = [...ofacAddresses, ...chainalysisAddresses];
for (const addr of allNew) {
await this.bloomFilter.add(addr.address.toLowerCase());
await this.db.upsertBlockedAddress({
address: addr.address.toLowerCase(),
reason: addr.reason,
source: addr.source,
});
}
}
}
Blocklist Data Sources
| Source | Type | Updates | Availability |
|---|---|---|---|
| OFAC SDN List | Sanctions | Several times per week | Free |
| EU Sanctions | Sanctions | When changed | Free |
| Chainalysis Sanctioned | Sanctions + darknet | Real-time | Paid |
| Elliptic Lens | Darknet, fraud | Real-time | Paid |
| Community lists (GitHub) | Scammers, phishing | By contribution | Free |
The OFAC SDN list contains crypto addresses — they need to be parsed from an XML file (SDN_Advanced.xml). Chainalysis and Elliptic provide broader lists via API.
Automatic Updates
// Cron: check for OFAC updates every hour
@Cron("0 * * * *")
async syncOFACList() {
const etag = await this.cache.get("ofac_etag");
const response = await fetch("https://www.treasury.gov/ofac/downloads/SDN_advanced.xml", {
headers: etag ? { "If-None-Match": etag } : {},
});
if (response.status === 304) return; // not changed
const xml = await response.text();
const addresses = parseOFACCryptoAddresses(xml);
await this.blocklist.updateAddresses(addresses, "OFAC");
await this.cache.set("ofac_etag", response.headers.get("ETag"));
this.logger.log(`OFAC sync: ${addresses.length} crypto addresses`);
}
Suspicious address blocking system with on-chain and off-chain components, automatic updates from OFAC and Chainalysis — 2-3 weeks development.