Stablecoin Development
When a request comes in saying "we need a stablecoin," the first question isn't "what price do we maintain?" but "what mechanism keeps the peg intact?" This determines everything: smart contract architecture, infrastructure requirements, regulatory risks, and operational complexity. Three fundamentally different architectures exist — each with its own conditions for viability.
Three Stablecoin Models
Fiat-Backed
The USDC/USDT model: 1 token = 1 dollar in a bank account. Technically simplest: minters mint upon receiving fiat, burners burn upon withdrawal. A central issuer acts as custodian.
Technical components: ERC-20 with role-based minting, blacklist (yes, USDC and USDT can freeze your address — contractual obligation to regulators), upgradeable proxy (Circle has updated the USDC contract several times).
Regulatory reality: in the EU, requires an EMI (Electronic Money Institution) license under MiCA since 2024. In the US, state money transmitter licenses in each state. Entry barrier: tens of millions of dollars in reserves and compliance.
Crypto-Backed
The DAI model (MakerDAO CDP model): user locks ETH/WBTC as collateral, receives DAI. Over-collateralization of 150%+ provides a buffer against volatility. When collateral price falls below liquidation threshold, the position is liquidated.
This is the most complex and architecturally interesting design from an engineering perspective.
Algorithmic
No peg to external assets — seigniorage mechanics or rebase. The history of algorithmic stablecoins is grim: Terra/Luna ($40B market cap → $0 in three days in May 2022), Basis Cash, Empty Set Dollar — all collapsed upon loss of confidence. A purely algorithmic stablecoin without any collateral backing — that's academic material, not production.
Detailed CDP Stablecoin Implementation
Let's focus on crypto-backed architecture — it's realistic for independent development and technically substantial.
Core contract structure
VaultManager — opening/closing positions, collateral management
PriceFeed — Chainlink oracles for collateral prices
LiquidationEngine — automatic liquidation of under-collateralized positions
StablecoinToken — ERC-20 stablecoin with controlled minting
StabilityPool — liquidator pool, they receive collateral at discount
FeeCollector — stability fee collection, treasury distribution
VaultManager: Opening a Position
contract VaultManager {
struct Vault {
uint256 collateralAmount; // ETH/WBTC locked
uint256 debtAmount; // minted stablecoins
address collateralToken;
uint256 lastFeeTimestamp;
}
mapping(address => mapping(address => Vault)) public vaults;
// Parameters by collateral type
mapping(address => CollateralParams) public collateralParams;
struct CollateralParams {
uint256 liquidationRatio; // e.g., 150% = 15000 (bps)
uint256 stabilityFeeRate; // annual rate, e.g., 0.5%
uint256 liquidationPenalty; // penalty on liquidation, e.g., 13%
uint256 debtCeiling; // maximum debt for this collateral
bool isEnabled;
}
function openVault(
address collateralToken,
uint256 collateralAmount,
uint256 stablecoinAmount // how many stablecoins to receive
) external nonReentrant {
CollateralParams memory params = collateralParams[collateralToken];
require(params.isEnabled, "Collateral not supported");
// Check that collateral ratio is sufficient
uint256 collateralValueUSD = _getCollateralValue(
collateralToken,
collateralAmount
);
uint256 requiredCollateral = (stablecoinAmount * params.liquidationRatio) / 10000;
require(collateralValueUSD >= requiredCollateral, "Insufficient collateral");
// Check debt ceiling
require(
totalDebt[collateralToken] + stablecoinAmount <= params.debtCeiling,
"Debt ceiling reached"
);
// Accept collateral
IERC20(collateralToken).transferFrom(msg.sender, address(this), collateralAmount);
// Update vault
Vault storage vault = vaults[msg.sender][collateralToken];
vault.collateralAmount += collateralAmount;
vault.debtAmount += stablecoinAmount;
vault.collateralToken = collateralToken;
vault.lastFeeTimestamp = block.timestamp;
totalDebt[collateralToken] += stablecoinAmount;
// Mint stablecoin to user
stablecoin.mint(msg.sender, stablecoinAmount);
emit VaultOpened(msg.sender, collateralToken, collateralAmount, stablecoinAmount);
}
}
Stability Fee: Continuous Accrual
Stability fee is an interest rate continuously accrued on debt. It serves as both a regulatory lever (raising fee → less minting → lower supply → price tends toward $1 under downward pressure) and a revenue source for the protocol.
function _accrueFee(address user, address collateralToken) internal {
Vault storage vault = vaults[user][collateralToken];
if (vault.debtAmount == 0) return;
CollateralParams memory params = collateralParams[collateralToken];
uint256 elapsed = block.timestamp - vault.lastFeeTimestamp;
// Continuous compounding: debt * (1 + rate)^t ≈ debt * (1 + rate * t) for small t
// Exact formula using natural logarithm:
uint256 feeMultiplier = _continuousCompound(params.stabilityFeeRate, elapsed);
uint256 newDebt = (vault.debtAmount * feeMultiplier) / RAY; // RAY = 1e27
uint256 fee = newDebt - vault.debtAmount;
vault.debtAmount = newDebt;
vault.lastFeeTimestamp = block.timestamp;
// Fee goes to protocol Surplus Buffer
surplusBuffer += fee;
stablecoin.mint(address(this), fee); // stablecoin is "created" as fee
}
Math: rpow(base, n, RAY) — precise integer exponentiation, from MakerDAO DSMath.
Liquidation Engine
contract LiquidationEngine {
// Collateral Ratio = (collateralValue / debtValue) * 100
function getCollateralRatio(
address user,
address collateralToken
) public view returns (uint256) {
Vault memory vault = vaultManager.getVault(user, collateralToken);
if (vault.debtAmount == 0) return type(uint256).max;
uint256 collateralValue = priceFeed.getPrice(collateralToken)
* vault.collateralAmount / 1e18;
return (collateralValue * 10000) / vault.debtAmount;
}
function liquidate(
address user,
address collateralToken,
uint256 debtToRepay
) external nonReentrant {
CollateralParams memory params = collateralParams[collateralToken];
uint256 cr = getCollateralRatio(user, collateralToken);
require(cr < params.liquidationRatio, "Vault is healthy");
// Liquidator repays part of debt, receives collateral at discount
// Example: repays $100 debt, receives $113 in ETH (13% bonus)
uint256 collateralToSeize = (debtToRepay
* (10000 + params.liquidationPenalty) // add penalty
* 1e18) / (priceFeed.getPrice(collateralToken) * 10000);
// Check we don't seize more than exists
Vault storage vault = vaults[user][collateralToken];
collateralToSeize = Math.min(collateralToSeize, vault.collateralAmount);
// Liquidator burns stablecoin to repay
stablecoin.burnFrom(msg.sender, debtToRepay);
vault.debtAmount -= debtToRepay;
vault.collateralAmount -= collateralToSeize;
// Liquidator receives collateral
IERC20(collateralToken).transfer(msg.sender, collateralToSeize);
emit Liquidation(user, collateralToken, debtToRepay, collateralToSeize);
}
}
Problem of rapid market crashes — if ETH price falls 30% in minutes (flash crashes happen), liquidators can't react fast enough, the system accumulates bad debt. Solution: Dutch Auction liquidations (like MakerDAO v2 Liquidations 2.0): auction price starts high and drops every few seconds, incentivizing liquidators to act faster.
Price Oracle: Critical Component
Stablecoin depends entirely on oracle reliability. Chainlink Data Feeds — the standard:
import "@chainlink/contracts/src/v0.8/interfaces/AggregatorV3Interface.sol";
contract PriceFeed {
mapping(address => AggregatorV3Interface) public priceFeeds;
uint256 public constant PRICE_STALENESS_THRESHOLD = 3600; // 1 hour
function getPrice(address token) external view returns (uint256) {
AggregatorV3Interface feed = priceFeeds[token];
(
uint80 roundId,
int256 price,
,
uint256 updatedAt,
uint80 answeredInRound
) = feed.latestRoundData();
require(price > 0, "Invalid price");
require(updatedAt >= block.timestamp - PRICE_STALENESS_THRESHOLD, "Stale price");
require(answeredInRound >= roundId, "Stale round");
return uint256(price); // 8 decimals for most Chainlink feeds
}
}
Never use spot price from Uniswap/Curve directly — flash loan attacks manipulate price in a single block. TWAP as backup oracle, Chainlink as primary.
Peg Maintenance Mechanisms
Arbitrage incentives — market-driven:
- Stablecoin price < $1: arbitrageurs buy cheap, repay debt (burn stablecoin), receive collateral → supply falls → price rises
- Price > $1: users mint new stablecoin (sell it) → supply grows → price falls
PSM (Peg Stability Module) — like MakerDAO: direct 1:1 swap between stablecoin and USDC for small fee. Hard anchor, but introduces USDC as a centralized asset anchor.
Dynamic Stability Fee — governance adjusts fee rate in response to price deviation. Slow mechanism (requires governance vote or automated policy).
Security and Known Attacks
Cream Finance Hack (2021, $130M) — flash loan attack on CREAM using their own token as collateral for themselves. Circular dependency in oracle + flash loan = drain. For CDP: collateral should not depend on stablecoin value.
Euler Finance Hack (2023, $197M) — vulnerability in depositing collateral without corresponding debt increase. Careful accounting invariant checking is mandatory: totalCollateral * price >= totalDebt * liquidationRatio must hold at any point after any transaction.
Invariant testing in Foundry — mandatory pattern:
// Invariant: protocol is always solvent
function invariant_solvency() public view {
uint256 totalCollateralValue = calculateTotalCollateralValue();
uint256 totalDebt = stablecoin.totalSupply();
assertGe(totalCollateralValue, totalDebt);
}
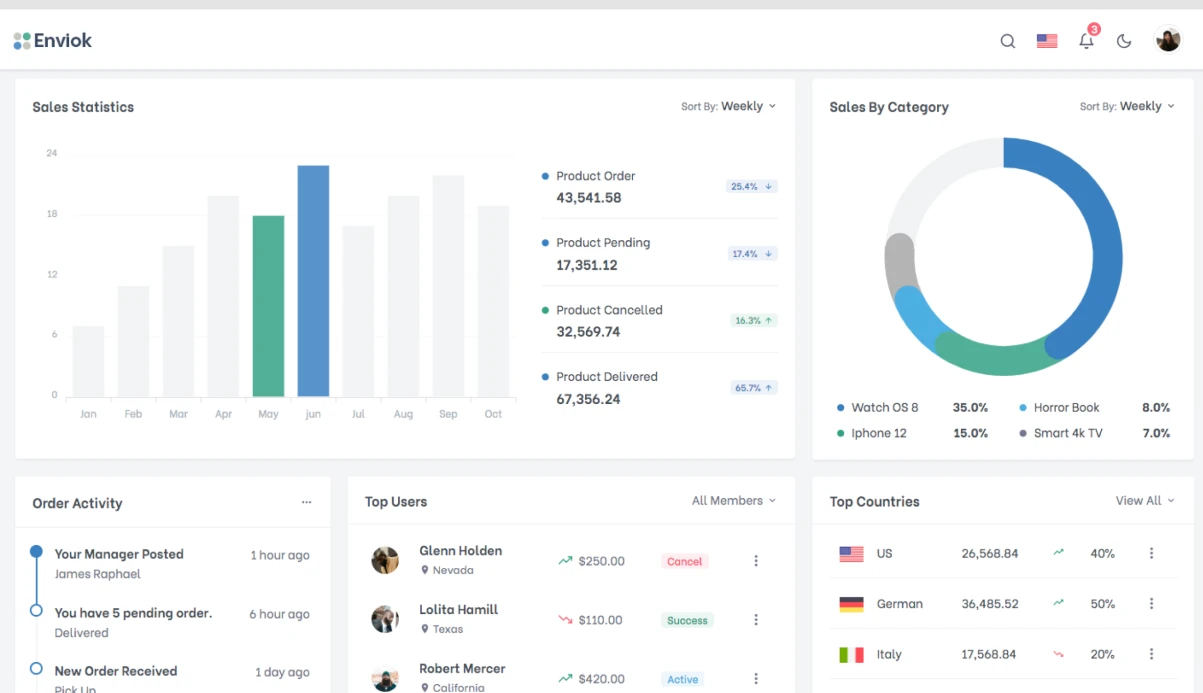
Timeline and Phases
| Phase | Content | Duration |
|---|---|---|
| Protocol design | Mechanics, parameters, tokenomics | 2–3 weeks |
| Core contracts | VaultManager, LiquidationEngine, PriceFeed | 4–6 weeks |
| Governance & parameters | TimeGovernor, parameter adjustment system | 2–3 weeks |
| Testing suite | Unit + fuzz + invariant tests | 3–4 weeks |
| Frontend interface | Vault management UI | 3–5 weeks |
| Audit | 1–2 audit firms | 4–8 weeks |
| Testnet + bug bounty | 4–6 weeks | |
| Mainnet (staged rollout) | Gradual increase of debt ceiling | 2–4 weeks |
Minimum realistic timeline to mainnet: 6–9 months. Two audits are not a luxury but a necessity: during 2021–2023, CDP protocols lost >$500M due to liquidation logic and oracle errors.